Latest research from the United States: An $800 device can intercept satellites and steal Bitcoin miner data.
A recent study by the University of California, San Diego and the University of Maryland has shocked the industry: it is possible to intercept Bitcoin Miner data transmitted from geostationary satellites using consumer-grade hardware costing only $800. The research shows that about 50% of GEO satellite downlinks are unencrypted, leaving Bitcoin miners using the Stratum V1 protocol at risk of passive eavesdropping on operational templates and miner IDs.
Academic research reveals satellite security black holes
The research team from the University of California, San Diego (UCSD) and the University of Maryland has made a shocking discovery. Their research report shows that approximately half of the data transmitted via downlink from geostationary orbit (GEO) satellites is not encrypted. Even more concerning is that the cost to reproduce such data interception is extremely low—only $800 for consumer-grade hardware.
According to a report by Wired magazine, the research team successfully captured various sensitive communications, including telecommunication backhaul data, industrial control traffic, and law enforcement communications. Researchers have reported to affected vendors and assisted in remediation wherever possible after discovering these vulnerabilities. The systems and networks group at the University of California, San Diego submitted a paper titled “Don't Look Up” to the Taipei CCS 2025 conference, indicating that this research has passed rigorous peer review and is not merely a laboratory whim, but a scientifically validated real threat.
It is worth noting that this study only covers a small portion of satellites visible from San Diego. Considering that the number of GEO satellites operating globally far exceeds the research sample, the actual risk exposure may be even more extensive. This finding serves as a wake-up call for various industries that rely on satellite communications, and Bitcoin miners, as a group that is highly dependent on internet connectivity, become a particularly noteworthy focus of this study.
Why Bitcoin Miners Become Targets
For Bitcoin miners and mining pools operating in remote areas, the risks revealed by this study directly map to a core operational issue: how to ensure secure transmission along the path carrying the Stratum protocol. Stratum is the key protocol connecting miners with mining pools, responsible for distributing work templates, collecting hash power shares and block candidates, guiding hash power, and determining the reward calculation method.
The historical deployment of Stratum V1 has a fatal flaw. Unless operators explicitly enable TLS encryption, Stratum V1 typically runs over plaintext TCP. This means that when satellites are used as a communication backhaul, the mining pool endpoints, miner identification codes, and job templates traverse the radio link in plaintext, making it easy for passive eavesdroppers to read this information.
The risks associated with this exposure are multifaceted. First, the leakage of miner identities and pool connection information could be used for targeted attacks or competitive intelligence gathering. Second, the visibility of operational templates allows attackers to understand the miner's workload distribution strategies, and they may even attempt share hijacking. Third, large-scale traffic monitoring could reveal the geographic distribution and hash power scale of mining farms, which could pose regulatory or tax risks in certain jurisdictions.
Stratum V1 vs V2: A World of Difference in Security
(Source: CryptoSlate)
The design of the Stratum V2 specification is precisely aimed at addressing the security flaws of V1. V2 is preset with a verified encryption mechanism, utilizing the Noise handshake protocol and AEAD (Authenticated Encryption with Associated Data) cipher. This design can completely eliminate the possibility of passive interception and enhance integrity protection, preventing share hijacking attempts that rely on manipulating upstream traffic.
According to the Stratum V2 security specification, mining operators can bridge old equipment through a translation proxy, which means that encryption sessions can begin without the need for firmware replacement on ASIC miners. This smooth migration path significantly reduces the technical barriers and cost pressures of upgrading.
It is worth clarifying that this satellite security discovery does not involve all “space Bitcoin” systems. Blockstream's satellite service broadcasts public Bitcoin block data in a one-way downlink format, and its satellite API supports encrypted messages from senders, which places it in a completely different category from GEO return links that transmit privately controlled traffic. According to Blockstream's explanation, the service is designed to enhance network resilience, allowing areas with poor network access to receive blocks, and does not carry miner credentials or miner-controlled session data. Blockstream's May network update confirmed ongoing operations and frequency adjustments, but this does not change the threat model of Bitcoin miners controlling the link.
Risk Quantification: How much hash power is exposed?
Budget pressures have made secure deployments critical. The current Bitcoin network hash rate hovers around 1.22 ZH/s (or 1,220 EH/s). According to recent miner economic data, the hash price at the end of September was about $51 per PH per day, while the forward curve for the first half of 2026 is expected to be between the low $40s and the high $50s. This income environment means operators will closely monitor operational costs, but it's worth noting that the primary cost of transmitting encryption is engineering time rather than new hardware, which reduces the resistance to short-term enhancements.
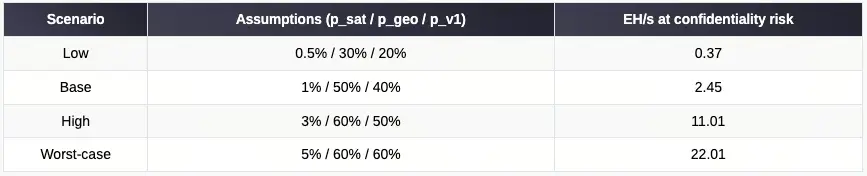
The research team established a simple risk model to quantify exposure levels. Let H represent the total hash rate (close to 1,223 EH/s), p_sat is defined as the share using satellite backhaul, p_geo is defined as the share of GEO rather than encryption LEO or ground connections, and p_v1 is defined as the share of Stratum V1 that is still operating without TLS. The risk hash rate equals H × p_sat × p_geo × p_v1.
According to the thermodynamic chart for Q4 2025 provided by the Hashrate Index, it can be inferred which regions rely more on satellite backhaul due to ground network limitations. The following scenarios illustrate the magnitude of risk exposure:
Low-Risk Scenario: Assuming 0.5% use satellites, 30% are GEO, and 20% are unencrypted V1, the exposed hash rate is approximately 0.37 EH/s.
Baseline Scenario: Assume 1% use satellite, 50% are GEO, and 40% are unencrypted V1, exposing computing power of approximately 2.45 EH/s.
High Risk Scenario: Assuming 3% use satellites, 60% are GEO, and 50% are unencrypted V1, the exposed hash rate is approximately 11.01 EH/s.
Worst Case Scenario: Assuming 5% use satellites, 60% are GEO, and 60% are unencrypted V1, exposing a computing power of up to 22.01 EH/s.
Even in a conservative benchmark scenario, an exposed hash rate of 2.45 EH/s accounts for approximately 0.2% of the entire network. This proportion may seem small, but in the highly competitive mining industry, any security vulnerability can translate into substantial economic losses or competitive disadvantages.
Operation Guide: How to Protect Bitcoin Miners
In the face of the threats revealed by this study, what specific measures should Bitcoin miners and mining pool operators take? Operational guidance directly follows the logic of the protocol.
First, enforce TLS encryption on all Stratum V1 endpoints and the routers in front of them. The TLS 1.3 handshake can be completed in one round trip, and measurements in production environments show that the CPU and network overhead of modern systems are low. In most deployments, the performance cost is limited, which eliminates the common objections regarding remote site monitoring delays and utilization.
Secondly, prioritize establishing new connections using the Stratum V2 protocol. In scenarios with hardware limitations, add an SV1→SV2 conversion proxy. According to the Stratum V2 specification, verified encryption can protect the confidentiality and integrity of channel messages, thereby eliminating the possibility of passive eavesdroppers easily obtaining satellite research records.
Third, the choice of return path is also very important. Although no transmission option can replace endpoint security hygiene, operators may consider avoiding traditional GEO satellites. Encrypted LEO (Low Earth Orbit) services or ground paths can reduce interception risks. When GEO must still be used, enforce encryption at every hop, disable insecure management interfaces on satellite modems, and monitor anomalies in shared modes and endpoint drift to detect signs of interference.
Remedial Cases of T-Mobile and Other Providers
Research from UCSD and UMD indicates that the cost of intercepting downlink channels is low and can be scaled using commercial hardware, undermining the assumption that radio links can evade notice due to their physical distance from adversaries. Providers, including T-Mobile, have begun addressing the related security issues following the researchers' disclosure of specific findings, suggesting that once visibility is established, remediation measures are indeed feasible.
This case provides important insights for Bitcoin miners: the window for patching security vulnerabilities is narrowing. As research tools penetrate and proof of concepts shift from academia to amateur communities, the strategy of relying on obscurity (security through obscurity) is becoming increasingly difficult to justify.
Key Path Selection for Next Year
The next year will determine the speed of the encryption transmission for mining pools and Bitcoin miners. The industry faces several potential development paths.
The first path is default secure: The mining pool only accepts V1 protocol via TLS and widely promotes the V2 protocol. The conversion proxy can smooth the transition of the old mining pool and compress the interception window. This is the most ideal scenario, significantly reducing the overall network's security risk in the short term.
The second path is gradual migration: leaving a large number of unencrypted or partially encrypted sites, thereby creating opportunities for participants with upstream link disruption capabilities. This incremental improvement, while better than doing nothing at all, will still maintain a considerable risk exposure for a significant amount of time.
The third path is to resist change: relying on ambiguity and refusing to upgrade. However, with the research results of the $800 interception device being made public, the risks of this path are rising rapidly.
These trajectories do not require protocol inventions, only deployment choices that are consistent with easily understandable original languages. TLS and Stratum V2 are both mature technologies whose security and performance have been validated on a large scale. What remains is simply a matter of willingness to execute and engineering resources.
Risk Differences of Node Operators
It is worth noting that the risk situation faced by Bitcoin node runners is different from that of Bitcoin miners. Nodes typically receive and transmit public blockchain data, rather than private credentials or payment instructions. Running a full node does not require transmitting sensitive authentication materials via satellite links, as the exchanged data, blocks, and transactions are designed to be public.
However, if nodes rely on GEO satellites for bi-directional internet access, any unencrypted TCP traffic will be subject to the same exposure: without transport encryption, peers, IPs, and message metadata may be observed or spoofed. Using encryption overlay networks like Tor, VPNs, or I2P can minimize this risk. Compared to Bitcoin miners using Stratum V1, node operators do not leak control traffic that carries value, but management interfaces and network tunnels should still be encrypted to prevent de-anonymization or routing interference.
This study clarifies one point for Bitcoin miner operators running on radio backhaul edges: currently, plaintext control traffic is easily observable, and encryption Stratum is a simple, low-overhead solution. The current operational path mandates TLS for V1, and then migrate to Stratum V2 as soon as possible. Delaying will only widen the risk exposure window, while taking action can immediately close this security vulnerability.