LiteLLM hacking incident: 500,000 credentials leaked, cryptocurrency wallets may be stolen, how to check if you're affected?
Author: HIBIKI, Crypto City
LiteLLM suffers supply chain attack, hundreds of GB of data and 500,000 credentials leaked
The AI open-source package LiteLLM, which has a daily download volume of up to 3.4 million, is an important bridge for many developers connecting multiple large language models (LLMs), but it has recently become a target for hackers. Kaspersky estimates that this wave of attacks has exposed over 20,000 code repositories to risk, and hackers claim to have stolen hundreds of GB of confidential data and over 500,000 account credentials, causing a serious impact on global software development and cloud environments.
After tracing back through cybersecurity experts, it was discovered that the source of the LiteLLM hacking incident was the open-source security tool Trivy, which many companies use to scan for system vulnerabilities.
This is a typical nested supply chain attack, where hackers target the upstream trusted tools relied upon by the target, quietly inserting malicious code, akin to poisoning the water supply at a water plant, causing all consumers to unknowingly fall victim.
Image source: Trivy | The source of the LiteLLM hacking incident turned out to be the open-source security tool Trivy, which many companies use to scan for system vulnerabilities.
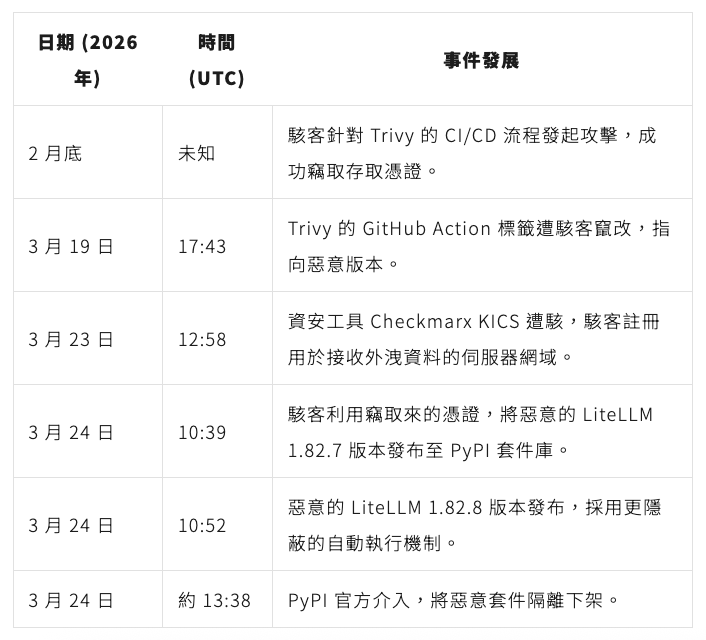
Full process of the LiteLLM attack: from security tool to AI package chain reaction
According to analysis by cybersecurity companies Snyk and Kaspersky, the LiteLLM attack incident had been brewing as early as the end of February 2026.
Hackers exploited a vulnerability in GitHub’s CI/CD (a process for automated software testing and deployment) to steal the access token of Trivy maintainers. Since the token was not fully revoked, hackers successfully tampered with Trivy’s release tags on March 19, allowing the automated process to download a scanning tool containing malicious code.
Subsequently, hackers used the same method to take control of LiteLLM’s release permissions on March 24 and uploaded versions 1.82.7 and 1.82.8 containing malicious code.
At this time, developer Callum McMahon encountered an issue while testing the Cursor editor’s extension, as the system automatically downloaded the latest version of LiteLLM, causing his computer resources to be instantly depleted.
Through AI assistance Debug, he discovered that the malicious code contained a flaw that unexpectedly triggered a fork bomb, which is a malicious action that continuously self-replicates and exhausts computer memory and computing resources, leading to the early exposure of this covert attack.
According to Snyk’s analysis, the malicious code in this attack is divided into three phases:
- Data Collection: The program fully scrapes sensitive information from the victim’s computer, including SSH remote connection keys, cloud service (AWS, GCP) access credentials, and seed codes for cryptocurrency wallets like Bitcoin and Ethereum.
- Encryption and Leakage: The collected data is encrypted and packaged, then secretly sent to a fake domain pre-registered by the hackers.
- Persistent Presence and Lateral Movement: The malicious program implants a backdoor in the system, and if it detects Kubernetes, an open-source platform environment used for automating the deployment and management of containerized applications, it will attempt to spread the malicious program to all nodes in the cluster.
Timeline of LiteLLM and Trivy supply chain attacks
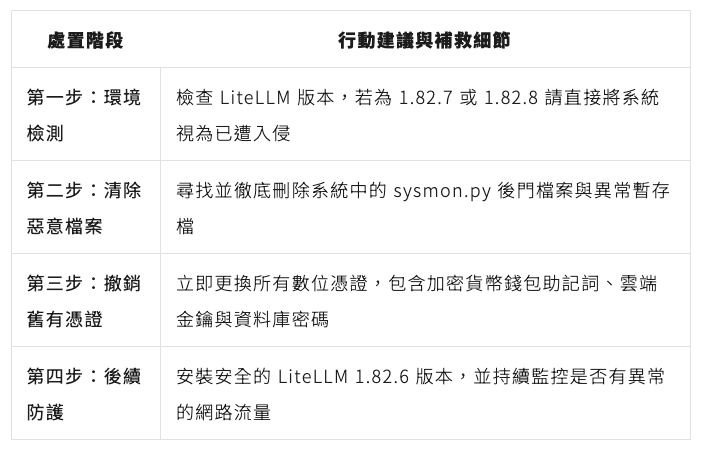
Is your wallet and credentials safe? Detection and remediation guide
If you have installed or updated the LiteLLM package after March 24, 2026, or if your automated development environment has used the Trivy scanning tool, your system is likely compromised.
According to Callum McMahon and Snyk’s recommendations, the primary task for protection and remediation is to confirm the extent of the compromise and thoroughly block the hackers’ backdoors.
Kaspersky recommends using the following open-source tools to enhance the security of GitHub Actions:
- zizmor: This is a tool for static analysis and detecting configuration errors in GitHub Actions.
- gato and Gato-X: These two versions of the tool are mainly used to help identify automated process pipelines with structural vulnerabilities.
- allstar: A GitHub application developed by the Open Source Security Foundation (OpenSSF), specifically designed to set and enforce security policies within GitHub organizations and repositories.
Behind the LiteLLM attack, hackers have already set their sights on the lobster farming craze
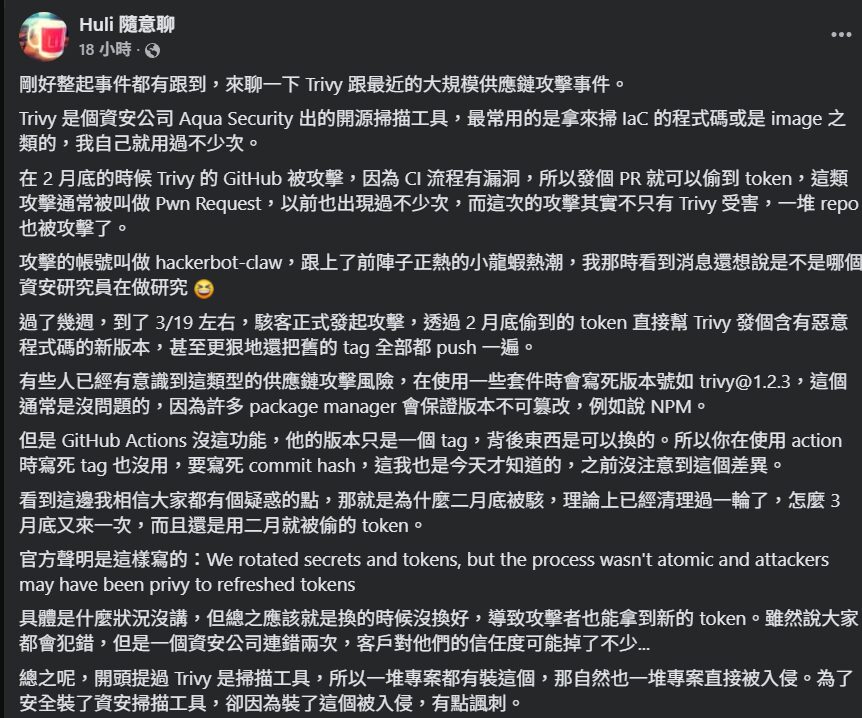
According to analysis by Snyk and engineer Huli, who focuses on cybersecurity, the mastermind behind this case is a hacker group called TeamPCP, which has been active since December 2025 and frequently establishes channels for activities through communication tools like Telegram.
Huli pointed out that during the attack process, hackers used an automated attack component called hackerbot-claw. This name cleverly aligns with the recent trend of AI agents in the AI community known as lobster farming (OpenClaw).
These hackers precisely targeted high-privilege and widely used infrastructure tools, including Trivy and LiteLLM, and understood how to leverage the latest AI trends to expand the scale of the attack, demonstrating highly organized and targeted criminal methods.
Image source: Huli Random Chat | Engineer Huli explains the Trivy and LiteLLM supply chain attack incident (partial screenshot)
With the proliferation of AI tools, permission control and supply chain security in the development process have become risks that all companies cannot ignore.
Cases such as the recent hacking of well-known developers’ NPM accounts, leading to the injection of malicious code into JavaScript packages, potentially impacting numerous DApps and wallets; or Anthropic revealing that Chinese hackers launched the first large-scale AI automated cyber espionage operation through Claude Code, should all serve as warnings.