OpenClaw Lands on AWS, Critical Security Vulnerability Exposes Over 40,000 Cloud Instances

Amazon Web Services (AWS) recently launched a one-click hosting deployment service for OpenClaw on its lightweight virtual server product, Amazon Lightsail, providing a simplified cloud deployment solution for this AI agent framework. However, this release coincides with ongoing security crises surrounding OpenClaw, with reports revealing 42,900 publicly exposed instances across 82 countries worldwide.
AWS Lightsail Hosting Deployment: Technical Details and Positioning
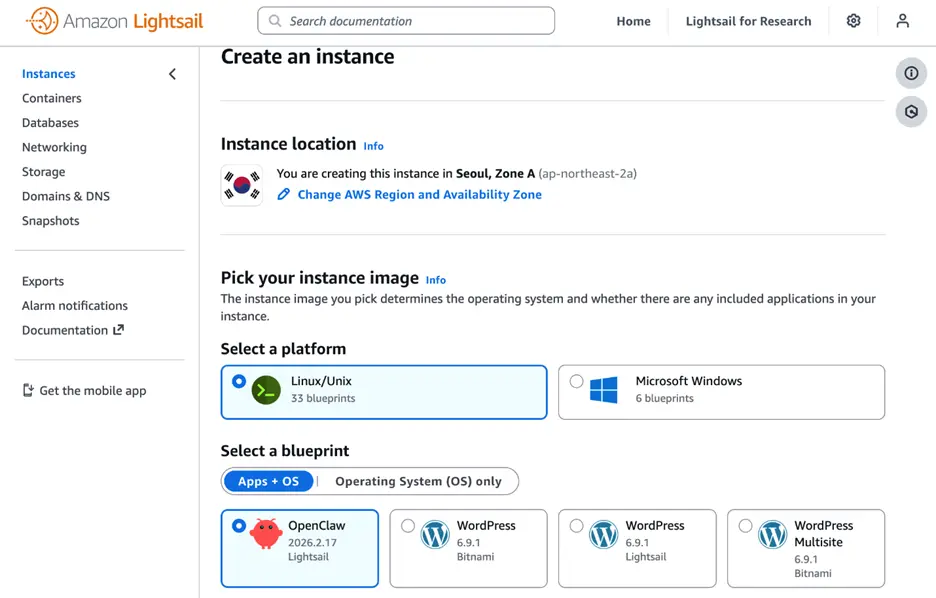
AWS states that this integration responds to widespread customer challenges in configuring OpenClaw independently. Lightsail blueprints are pre-configured with Amazon Bedrock (default integration with Claude Sonnet 4.6) and automatically set up the necessary IAM roles via CloudShell scripts. After selecting the OpenClaw blueprint, users can interact with the AI agent through a browser and SSH credentials, using platforms like WhatsApp, Telegram, Slack, Discord, or web interfaces.
From a popularity perspective, OpenClaw’s rise has been rapid: created by Peter Steinberger in November 2025 (initially named Clawdbot, later renamed Moltbot and OpenClaw twice), it went viral in early 2026, accumulating 100,000 stars within weeks. It has now surpassed Linux and React to become the repository with the most stars among non-aggregated projects on GitHub. Steinberger joined OpenAI in February this year, and OpenClaw has since transitioned into an independent open-source foundation funded by OpenAI.
CVE-2026-25253 and Large-Scale Instance Exposure: The Full Security Landscape
The core security challenge AWS faces with this release is a well-documented severe vulnerability and its resulting widespread exposure:
CVE-2026-25253 (disclosed February 1, 2026): Affects all OpenClaw deployments prior to version 2026.1.29, allowing attackers to execute remote code with a single command by stealing WebSocket tokens. Malicious URLs can be crafted so that, when clicked by users, authentication tokens are automatically sent to attacker-controlled servers without any additional user action.
Exposure Scale Statistics: Hunt.io identified over 17,500 exposed instances; Bitsight recorded over 30,000 between January and February; SecurityScorecard’s global scans confirmed 42,900 public instances, with 15,200 confirmed to have RCE vulnerabilities.
Cloud Deployment Concentration: 98.6% of exposed instances run on cloud platforms like DigitalOcean, Alibaba Cloud, Tencent Cloud, and AWS, rather than home networks, indicating widespread use in enterprise and developer environments.
Credential Theft Targets: Each OpenClaw instance stores API keys for services like Claude, OpenAI, and Google AI, making them high-priority targets for credential theft.
Government responses are also emerging: China’s Ministry of Industry and Information Technology issued security warnings, and South Korean tech companies have banned internal use of OpenClaw.
Supply Chain Pollution and Structural Security Risks
Beyond known vulnerabilities, security researchers have uncovered deeper systemic issues:
ClawHub Supply Chain Pollution: Bitdefender found approximately 900 malicious packages within OpenClaw’s skill center ClawHub, accounting for 20% of all published skills. These malicious packages include credential-stealing tools disguised as utilities, backdoors providing persistent access, and advanced malware with obfuscated payloads to bypass code review. OpenClaw skills run with system-level privileges, allowing direct access to messages, API keys, and files, making supply chain attacks far more destructive than those in ecosystems like npm or PyPI.
Prompt Injection Attacks: Research by Giskard shows that carefully crafted prompts can extract API keys, environment variables, and private credentials from running agents—a fundamental architectural issue that sandbox mechanisms provided by Lightsail blueprints cannot fully resolve.
AWS documentation admits that “running OpenClaw improperly may pose security threats,” and recommends not exposing gateways publicly, rotating tokens regularly, and storing credentials in environment variables rather than configuration files—yet, these guidelines lack comprehensive security reinforcement instructions.
Frequently Asked Questions
Can the security measures provided by AWS Lightsail protect OpenClaw users from known vulnerabilities?
Lightsail blueprints offer sandbox execution, device pairing authentication, and automatic TLS/HTTPS access, which mitigate some attack vectors. However, they cannot address vulnerabilities like CVE-2026-25253 that require upgrading to specific versions (AWS documentation should specify version requirements). They also do not fundamentally resolve prompt injection or ClawHub supply chain pollution issues.
Should enterprises deploy OpenClaw in production environments?
Token Security’s research shows that 22% of organizations have employees running OpenClaw without IT authorization, creating “shadow AI” deployments. Before adopting the AWS Lightsail-hosted version, organizations should thoroughly evaluate: (1) whether they have upgraded to a version patched against CVE-2026-25253; (2) whether all ClawHub skills are from trusted sources; (3) whether system-level permissions (file access, script execution, browser control) align with organizational security policies.
Has the security improved since OpenClaw transitioned to an open-source foundation?
OpenClaw has now become an independent open-source foundation funded by OpenAI, with MIT-licensed community maintainers continuing development. The foundation structure theoretically offers more sustainable governance and reduces risks associated with single maintainers. However, issues like ClawHub supply chain pollution reflect systemic gaps in ecosystem review mechanisms, requiring the foundation to establish stricter package review processes—simply changing organizational structure cannot fully resolve these systemic problems.