What Is Cysic (CYS)? A Guide to the ZK Proof Compute Network
As Ethereum’s scaling roadmap increasingly shifts toward ZK Rollups, zero-knowledge proofs are evolving from a niche cryptographic concept into a core component of blockchain infrastructure. Their applications now span transaction validation, privacy-preserving computation, and even verifiable AI, with their scope continuing to expand.
However, one major bottleneck remains: proof generation is extremely compute-intensive. While verification requires minimal resources, generating proofs often demands significant GPU power or even specialized hardware. This imbalance severely limits the scalability of ZK systems. Against this backdrop, a “ZK compute layer” is emerging as critical infrastructure. The ability to generate proofs more efficiently and at lower cost may define who controls the next wave of core resources in Web3.
What Is Cysic?
Cysic is a decentralized ZK prover network designed to provide high-performance proof generation as a service for blockchain and AI applications. Its core objective is to transform the traditionally complex and expensive process of generating ZK proofs into a schedulable, scalable compute network governed by market dynamics.
Put simply, Cysic functions like a compute network for ZK. If Bitcoin miners are seen as providers of computational power for block production, then Cysic’s prover nodes act as providers of computational power for proof generation. Users submit compute requests, the network schedules execution, and settlements are completed automatically, forming a full-fledged compute economy.
Cysic Core Architecture Explained
Cysic’s architecture consists of four key components that together form a complete ZK compute infrastructure.
First is the Prover Network, a globally distributed set of compute nodes responsible for executing proof generation tasks. Second is the Task Scheduler, the system’s coordination layer, which assigns tasks based on factors such as compute capacity, latency, and cost.
Once computation is complete, the Verifier module validates the generated proofs to ensure correctness and security. Finally, the Proof Market connects supply and demand, enabling proof generation capabilities to be priced and traded in a market-driven manner. Together, these components make Cysic not just a compute network, but a full compute marketplace.
How Does Cysic Work?
At its core, Cysic follows a standardized proof production pipeline. Users begin by submitting tasks that require proof generation, such as computation requests from ZK Rollups or other applications. These tasks are then routed through the scheduling system, which assigns them to the most suitable prover nodes.
After receiving a task, nodes use hardware resources such as GPUs or ASICs to run zk-SNARK or zk-STARK algorithms and generate proofs. The results then enter the verification phase, where correctness is confirmed. Once verified, the system completes settlement: users pay fees, and compute providers receive rewards.
The key innovation lies in breaking down complex computation into distributed tasks executed across the network. This enables parallel processing and cost optimization, significantly improving scalability.
Hardware Advantage: GPU vs ASIC
In ZK computation, hardware choice directly impacts both performance and cost structure. Traditionally, GPUs have been widely used due to their flexibility and ability to handle diverse workloads. However, that flexibility comes at the expense of peak efficiency, and long-term costs can remain high.
ASICs, on the other hand, are specialized chips designed for specific computational tasks. In ZK proving, they can deliver orders-of-magnitude performance improvements. One of Cysic’s defining features is its integration of custom ZK ASICs, mirroring the evolution seen in Bitcoin mining from GPUs to ASICs. As the network scales, ASICs can significantly reduce the cost per proof while also creating strong technical and hardware barriers to entry.
| Dimension | Cysic | Succinct |
|---|---|---|
| Positioning | Prover Network | Prover Service Layer |
| Hardware Strategy | GPU + ASIC | Primarily GPU |
| Architecture | Decentralized Network | Service-based Infrastructure |
| Scalability | High (network-based) | Medium |
| Differentiation | ASIC + Scheduling System | Developer tools and services |
CYS Token Model and Utility
CYS serves as the core value layer within the Cysic network, fulfilling multiple roles including payment, incentives, and governance. Users pay CYS to generate proofs, while prover nodes earn token rewards by completing tasks, forming the foundation of the network’s economic loop.
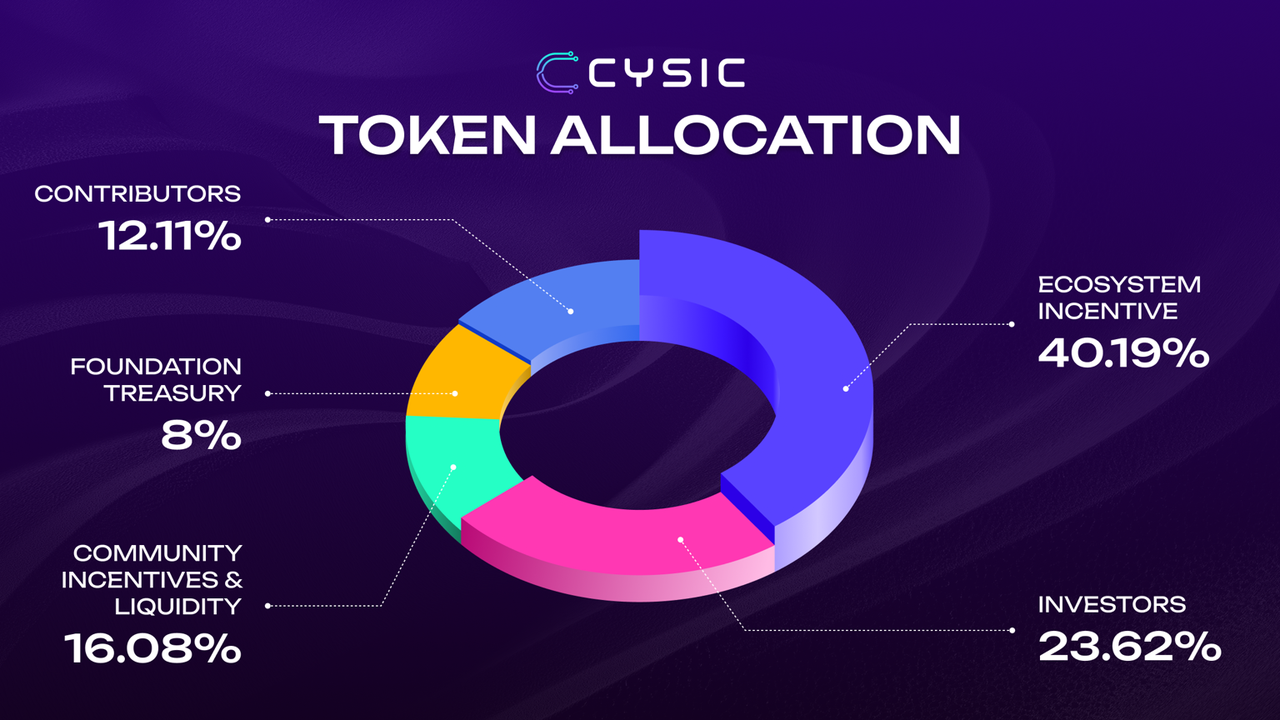
In addition, CYS can be used for governance, allowing holders to influence protocol parameters and future development. From a value perspective, Cysic’s growth is closely tied to demand for ZK computation. As ZK applications expand and proof demand increases, the need for compute resources rises accordingly, driving usage and value of CYS in a reinforcing cycle.
Cysic vs Succinct: A Comparative Analysis
Within the ZK prover space, Succinct is a notable comparable project. The key differences lie in positioning and technical approach. Cysic focuses on building a fully decentralized compute network, scaling through scheduling systems and hardware optimization. Succinct, by contrast, operates more at the service layer, offering developers tools and solutions for proof generation.
| Dimension | Cysic | Succinct |
|---|---|---|
| Positioning | Prover Network | Prover Service Layer |
| Hardware Strategy | GPU + ASIC | Primarily GPU |
| Architecture | Decentralized Network | Service-Oriented Infrastructure |
| Extensibility | High (Networked) | Medium |
| Differentiation | ASIC + Scheduling System | Developer Tools and Services |
From a hardware perspective, Cysic strengthens its performance edge through ASIC integration, while Succinct primarily relies on GPU optimization. Architecturally, Cysic’s network-based design offers greater scalability potential, whereas Succinct excels in developer experience and service integration.
Use Cases of Cysic
Cysic’s compute network supports a range of key applications. In blockchain, it provides efficient proof generation for ZK Rollups, improving Layer2 performance. In privacy computing, ZK technology enables data to be verified without being revealed, with Cysic supplying the required computational power.
As AI advances, verifiable AI is emerging as a critical direction, where ZK proofs ensure the trustworthiness of AI inference results. Additionally, in decentralized identity (DID) systems, ZK is used for privacy protection and identity verification. Looking ahead, the convergence of ZK and AI is likely to become a major driver of compute demand.
Advantages and Potential Risks of Cysic
Cysic demonstrates strong forward-looking positioning in both its chosen domain and technical approach. By focusing on the high-barrier field of ZK proving and leveraging ASICs alongside a decentralized network, it builds a foundation for long-term competitive advantage. Its alignment with both ZK and AI trends further strengthens its narrative potential.
At the same time, risks remain. ASIC development involves long cycles and significant capital investment, while the broader ZK ecosystem is still in its early stages, leaving demand growth uncertain. As interest in the sector increases, competition from other compute networks and infrastructure providers is also intensifying.
Conclusion
Overall, Cysic can be seen as foundational compute infrastructure for the ZK era. By decomposing proof generation into schedulable computational tasks and combining distributed networks with specialized hardware, it shifts ZK computation from a high-cost process to scalable production.
If ZK becomes the dominant technological path for blockchain, then compute infrastructure will serve as a critical backbone, and Cysic represents an important step in that direction.
FAQs
What is the CYS token used for?
It is primarily used for paying proof generation fees, incentivizing nodes, and participating in governance.
How is Cysic different from traditional cloud computing?
Cysic distributes compute resources through a decentralized network with token incentives, whereas traditional cloud services rely on centralized providers.
Why does ZK require specialized compute?
Because proof generation is computationally complex and demands extremely high hardware performance.
What is Cysic’s core advantage?
Its combination of ASIC hardware and a decentralized scheduling system enables significant performance and cost optimization.
Related Articles

Blockchain Profitability & Issuance - Does It Matter?
An Overview of BlackRock’s BUIDL Tokenized Fund Experiment: Structure, Progress, and Challenges

In-depth Analysis of API3: Unleashing the Oracle Market Disruptor with OVM

What is Fartcoin? All You Need to Know About FARTCOIN

Smart Money Concepts and ICT Trading


