Crypto’s most ridiculous robbery? A hacker minted $1 billion in DOT tokens, but only stole $230k
Hackers exploited a vulnerability in the Hyperbridge cross-chain bridge to mint 1 billion DOT tokens out of thin air. Although the token face-value amounted to 1.19 billion USD, due to severe market liquidity shortage, they ultimately cashed out only about 237k USD.
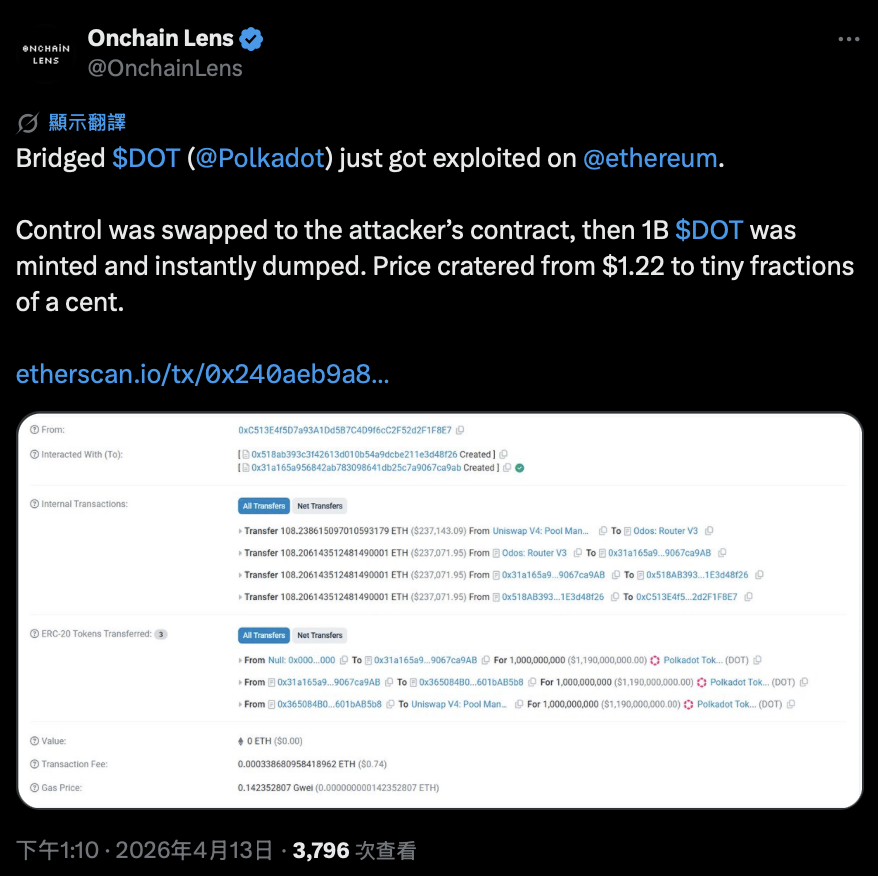
Crypto attack incidents are constantly happening, but cases like this—“taking a big risk for small profits”—are really rare. Earlier today (the 13th), a hacker exploited a vulnerability in the Hyperbridge cross-chain bridge to mint 1 billion Polkadot (DOT) tokens out of thin air on Ethereum. The token’s nominal value reached as high as 1.19 billion USD. However, when he tried to sell these tokens, severe liquidity shortage meant he ultimately swapped for only about 237k USD worth of Ethereum.
What needs clarification is that the target of the hacker attack was the “cross-chain bridge smart contract,” so the native DOT tokens on the Polkadot mainnet were not affected. The root cause of this vulnerability was that Hyperbridge’s EthereumHost contract failed to properly verify the authenticity of the message before passing the cross-chain message to TokenGateway.
Image source: X/@OnchainLens
Cross-chain bridges have always been the most vulnerable link in blockchain architecture, because they hold the administrative permissions for token contracts. Once the verification mechanism has a loophole, hackers can easily gain the power to mint tokens infinitely.
Attack method: Forging messages, taking over admin permissions, minting infinitely
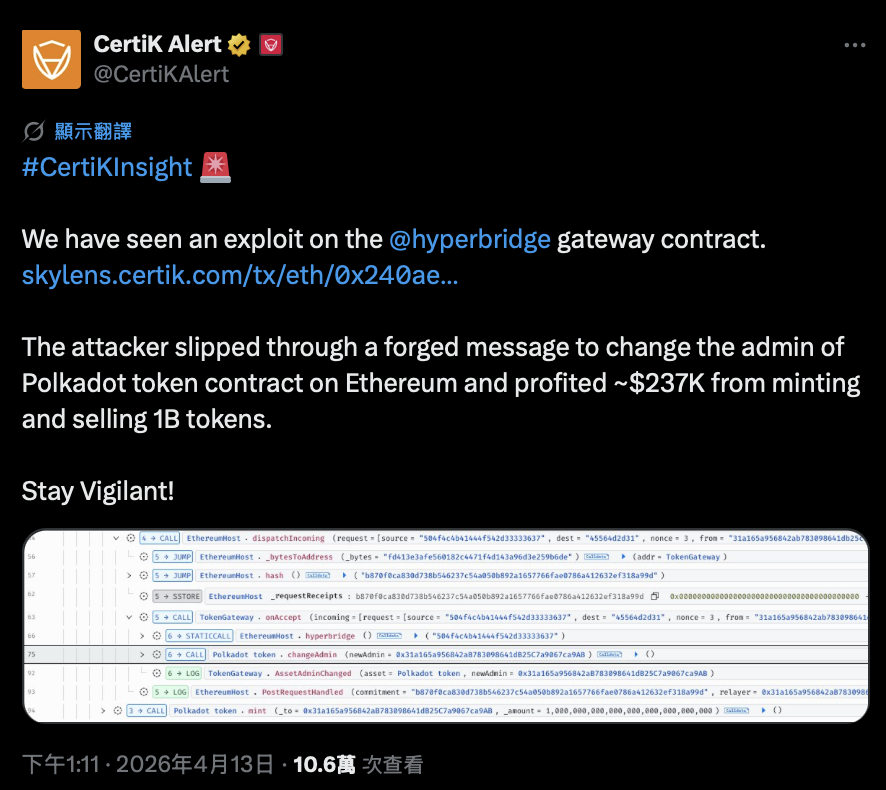
On-chain tracking shows that the hacker submitted a forged message via dispatchIncoming and successfully routed it to TokenGateway.onAccept. The system was supposed to verify the authenticity of this message based on the state on the Polkadot chain, but the verification mechanism recorded the commitment value as “all zeros.” This means the verification process was completely bypassed or did not exist at all, so the system mistakenly treated this fake message as a valid instruction.
The accepted message then immediately executed the changeAdmin function on the Polkadot token bridge contract, transferring administrative rights to the attacker’s address. After obtaining the admin permissions, the attacker minted 1 billion DOT tokens in a single transaction and dumped these tokens into Uniswap V4’s DOT-ETH trading pool via Odos Router V3. After multiple swaps at slightly different prices, they ultimately extracted about 108.2 ETH.
“Insufficient liquidity” turned into a protective shield
In financial markets, “insufficient liquidity” is usually the nightmare of big whales, but ironically, this time, insufficient liquidity became an invisible protective shield, greatly limiting the attacker’s profit potential.
Because the DOT liquidity depth on Ethereum is extremely limited, it was impossible to absorb the 1 billion tokens that were minted out of thin air. When the attacker rushed to sell and cash out, severe slippage caused the actual price of each token to be less than even 1 cent.
If this same vulnerability were on a more liquid, or higher-value, bridged asset, it would likely result in losses dozens of times greater. As of the time of writing, the DOT trading price is about $1.17, down 5% over the past 24 hours.
This incident once again shows that even if hackers have “infinite minting rights,” whether they can successfully arbitrage still depends on market liquidity and trading depth. The well-known blockchain security firm CertiK subsequently confirmed the attack and stated that the attacker profited about 237k USD by minting and selling the bridged tokens.
As of now, Hyperbridge’s official team has not issued any public comments regarding the hacker incident.
Image source: X/@CertiKAlert
- This article is reprinted with permission from: “Blocker”
- Original title: “The dumbest robbery? Hacker mints $1 billion of $DOT, but only steals $230k for ‘this reason’”
- Original author: Block Sister MEL
Related Articles
Fake Ledger Live App Steals $9.5M From 50+ Users Across Multiple Blockchains
Criticized for freezing USDC too slowly! Circle CEO: We will definitely wait for the court’s order before freezing—refusing to freeze privately/by ourselves without authorization
Attacker Exploiting Bridged Polkadot Vulnerability Transfers $269K to Tornado Cash
Bitcoin Developers Propose BIP 361 to Protect Against Quantum Computing Threats
Hackers Exploit Obsidian Plugin to Spread PHANTOMPULSE Trojan with Blockchain C2
Zerion Hot Wallet Loses $100K in AI-Driven Social Engineering Attack by North Korea-Linked Hackers