How Does Grass Work? Understanding Grass’s Bandwidth Sharing Reward Mechanism
As demand grows rapidly for AI model training, search engine indexing, and web data analysis, access to public internet data is becoming an important layer of infrastructure. Traditional data collection networks, however, often rely on centralized proxy services. These services can be costly, and they also raise issues such as concentrated access points and opaque resource allocation.
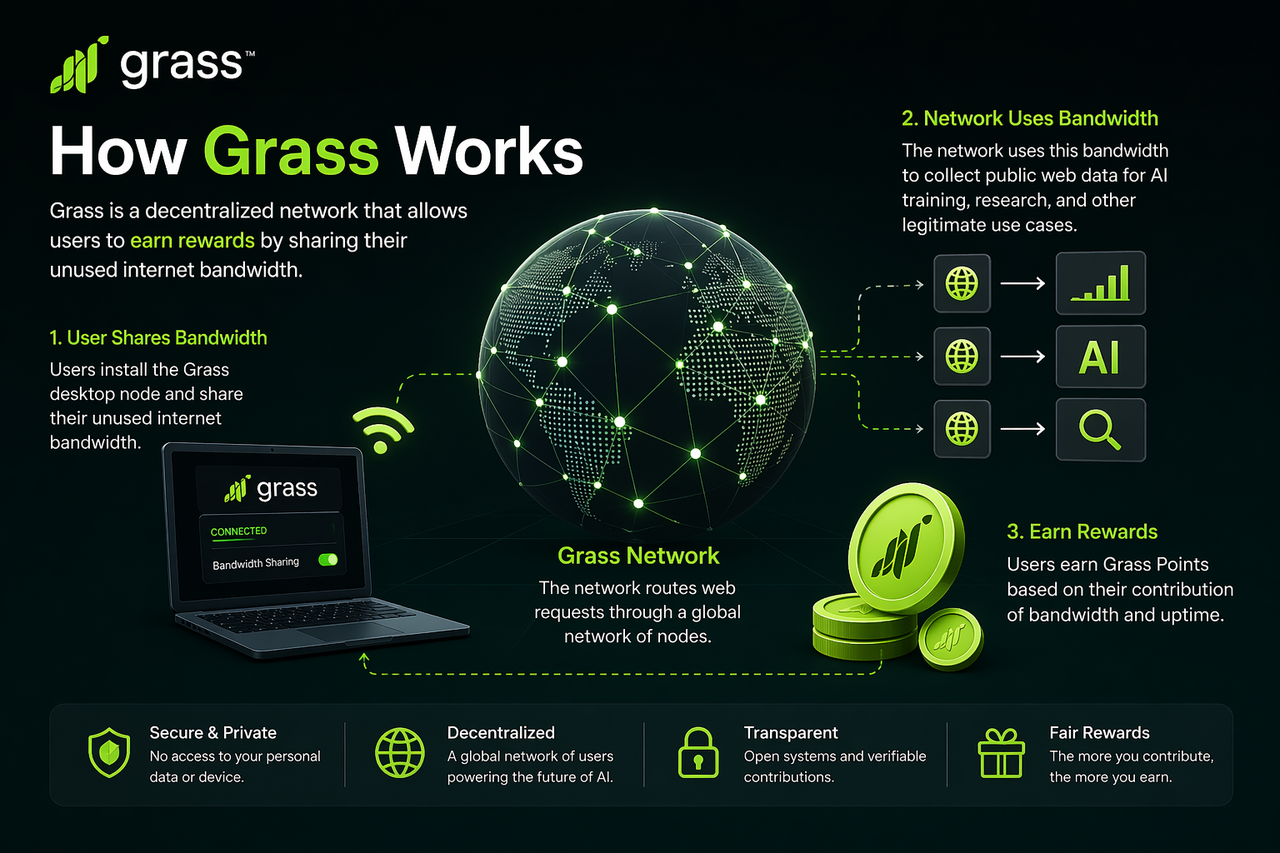
Grass was created to address this problem. By aggregating unused bandwidth from ordinary users, it builds a distributed network access layer that allows data requests to be completed through decentralized nodes, reducing reliance on centralized bandwidth providers. In this way, internet bandwidth becomes a shareable, verifiable, and incentivized network resource.
What Role Does Grass Play in Decentralized Infrastructure?
Within decentralized infrastructure, Grass serves as a “distributed bandwidth supply network.” It connects two types of participants: ordinary users with unused bandwidth, and service demand parties that need access to public web data.
Grass is important because it turns personal network resources that were previously difficult to quantify or use directly into infrastructure resources that can participate in protocol operations. Through node verification, traffic distribution, and points based incentives, Grass enables ordinary users to contribute to the underlying network supply. This model is similar to “sharing hard drive space” in decentralized storage networks, except Grass shares “network bandwidth.”
What Is the Basic Workflow of Grass?
Grass operates through four main steps: user node connection, bandwidth contribution verification, network task distribution, and reward point allocation.
First, users connect to the network by installing Grass node software. Once a node is online, the system checks the node’s available network resources and confirms that it can maintain a stable connection.
Next, the Grass network verifies the node’s status, including online time, bandwidth quality, and accessibility, to ensure that the node can provide effective network services. After passing verification, the node is added to the pool of callable resources.
Then, when data access requests appear in the network, Grass assigns tasks to eligible nodes, which complete public web access requests on behalf of the network.
Finally, the system records points based on node contribution, including online time, task processing volume, and node stability, then distributes reward points to users.
Together, these steps create a complete resource contribution loop, allowing user bandwidth to be continuously converted into contribution value within the protocol.
How Is User Shared Bandwidth Used?
Grass nodes do not contribute all network traffic, but rather the unused bandwidth resources on a user’s device. Network demand parties access public web data through Grass’s distributed nodes instead of sending requests directly through centralized servers.
The core advantage of this model is that traffic sources are more distributed. When a large number of nodes participate in network requests, data access requests are completed across different regions and network environments, improving the resilience and coverage of the data collection network.
For users, Grass makes use of idle resources. Node contribution therefore does not directly change the purpose of their internet connection, but provides additional network services within the available bandwidth range. Grass node resources are mainly used to distribute public web requests, not to access private files or personal data stored on users’ local devices.
How Is the Grass Node Reward Mechanism Calculated?
Grass’s reward mechanism is essentially a points model based on network contribution. The more stable a node’s contribution and the longer it participates, the more points it will usually record. However, the actual number of points still depends on node quality, task demand, and protocol rules.
Rewards are mainly affected by three factors:
The first is online time. The longer a node stays online, the greater its chance of being assigned tasks, so online time forms the foundation of rewards.
The second is node quality. If a node has a stable connection and fast response speed, it can complete tasks more efficiently and is more valuable to the network, so it may receive a higher weighting.
The third is actual task contribution. Nodes that complete more valid network requests accumulate more contribution points.
This mechanism ensures that rewards are tied to actual contribution, creating ongoing incentives for node operators to provide bandwidth resources over the long term. It is important to note that points only represent a record of node contribution. Their value and future use depend on Grass protocol rules and do not constitute a guaranteed return.
How Does Grass Verify That Node Contributions Are Real and Valid?
One of the biggest challenges in a bandwidth sharing network is ensuring that node contributions actually exist. Grass addresses this through node status verification and task completion verification.
Node status verification confirms whether a node is online and whether its network is available, preventing invalid nodes from occupying the resource pool.
Task completion verification records how nodes execute tasks and confirms whether they have actually processed network requests. Only verified valid contributions are counted toward reward points.
This verification mechanism reduces the possibility of fake contributions and helps ensure that Grass’s incentive system is built on verifiable resource contribution.
How Is Grass Different from Traditional Proxy Networks?
Traditional proxy networks are usually built by centralized service providers that deploy servers and sell access capacity. Resource supply and revenue distribution are controlled by the platform, making it difficult for ordinary users to participate as resource providers.
Grass differs because its resource sources are decentralized. Bandwidth is provided collectively by user nodes, while the protocol is responsible for verification and task distribution, rather than having a single service provider control all resources.
This structure gives Grass two key characteristics: broader resource distribution and more transparent reward allocation. Ordinary users can participate in the network as resource providers, not just as service users.
Conclusion
Grass aggregates users’ idle bandwidth resources to build a verifiable and incentivized decentralized bandwidth sharing network. Its core mechanism includes node connection, bandwidth verification, task distribution, and points rewards, enabling ordinary users to participate in distributed data access infrastructure by contributing network resources.
This model not only increases the decentralization of public web data access, but also provides a new incentive method for network resource sharing. From the perspective of DePIN, or decentralized physical infrastructure networks, Grass turns unused bandwidth into a verifiable network resource, allowing ordinary users to take part in building decentralized network infrastructure.
FAQs
What Is the Core Function of Grass?
The core function of Grass is to let users share unused bandwidth resources, provide distributed connectivity for decentralized data access networks, and reward contributors through a points mechanism.
Where Do Grass Rewards Come From?
Grass rewards come from nodes’ contributions to network resources, including online time, network quality, and task processing volume. The system distributes points based on contribution.
Does Grass Use All Network Resources?
No. Grass uses the idle bandwidth resources on a user’s device and only participates in network task distribution within the available capacity.
How Is Grass Different from Traditional Proxy Services?
Traditional proxy services provide resources through centralized service providers, while Grass relies on user nodes to collectively provide bandwidth resources. This makes resource supply more distributed and the incentive mechanism more transparent.
Why Is Grass’s Verification Mechanism Important?
The verification mechanism ensures that node contributions are real and valid. It prevents fake online status or invalid tasks from affecting reward allocation and is an important foundation for the normal operation of a bandwidth sharing network.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?